Deloitte Data Breach: What Were They Thinking?
Let me make this clear right from the off, this isn’t another blog merely hammering an organisation that has had the misfortune to suffer a breach, that would be as churlish as it is stupid. The reality is a breach could probably occur to almost anyone and taking delight in the failure of a company to prevent one shows a degree of naivety in this industry.
The reason this particular breach caught my attention and got my back up is because Deloitte claim to be one of the biggest Cyber Security strategy advisers on the planet. They are a beacon of our industry, pioneers and leaders, the trendsetters, a brand that preaches and inspires many organisations on Cyber Security best practices.
What an Epic Fail
How then could they have failed so badly in their duty to implement some of the very basic elements of Cyber Security best practice that you would expect as a given from an organisation such as Deloitte.
Since the story was reported in the Guardian, security blogger Brian Krebs has been writing about what happened and how it happened.
In short, it turns out that an administrator account had become compromised and as a result the entire internal email database had been accessed, potentially along with confidential client information.
Have Deloitte Heard of Multi Factor Authentication?
It will come as shock to those who are genuinely passionate about Cyber Security to hear, according to Krebs’ source, that Deloitte had no Multi Factor authentication toolset in place. Once the Admin account was breached the hackers easily gained access to all internal email addresses and potentially client confidential information. How on earth was one single account given so many privileges to access everything without the need to question?
Also, what happened to some very basic IP Address white listing at least? Surely if an account with such privileges did have such levels of access you would do your best to ensure that it could only be used from a list of strictly approved locations?
Behaviour Analytics
Did Deloitte even have anything in place that could potentially spot the anomalous behaviour and alert their system administrators before it became a major incident? It’s not as though the act of exfiltrating an entire email database is hard to spot, even with the most basic of BA tools. Again something I would have expected Deloitte to have heavily invested in.
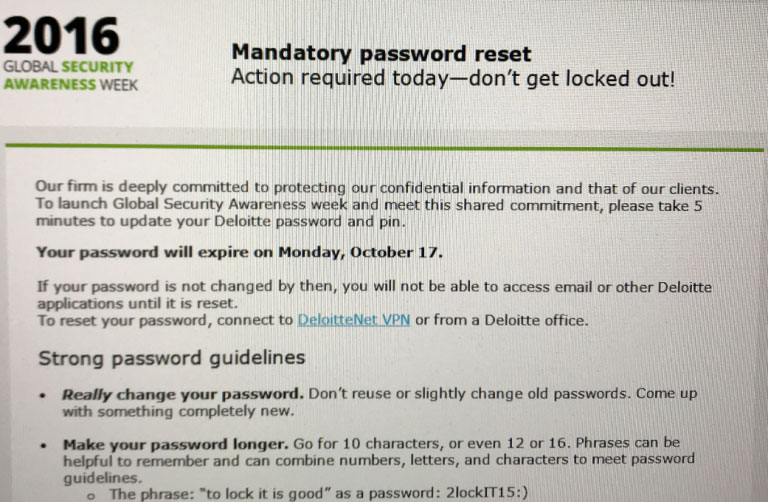
Deloitte must have known something was awry back in October 2016 when they sent a mandatory password reset notification to all US employees.
As expected they downplayed the incident by stating “very few” clients had been exposed. But to someone who handles the number of clients on the scale of Deloitte, what number equates to “very few”?
It is not the fact that they were breached that concerns me so much, it is not even the number of stolen credentials, it is more about how it occurred and how at the very heart of this issue it seems that Deloitte are not practising what they preach.
The Response
Nobody should be angered by the fact that Deloitte got breached, as I said, this could happen to anyone. We can only take the best possible preventative measures but nothing can be guaranteed to be 100% water tight, if anyone tells you this then politely send them on their way.
People, however, should be angered by the seemingly lackadaisical strategy deployed by one of the biggest purveyors of Cyber Security services and the negative impact that this will have on our industry. One thing that is evident to me from this breach is that the level of an organisations expertise is not mutually exclusive to its scale and brand. But, it is these big players at the forefront of our industry that set the standard by which we are all judged.
Now all we can do is wait and see how Deloitte respond, I would expect them to have a robust incident response program in place but in light of recent events this remains to be seen. How they respond will ultimately be where they are judged from here on in.
The joke doing the rounds on social media at the moment is that its time for Deloitte to call in the auditors!
We wait with bated breath and until then we have every right to be angry because this breach affects us all.
Danny Maher – CTO @HANDD
Danny Maher is CTO for HANDD Business Solutions and has recently authored the advisory paper Securing the Journey of Your Data.